Cybercrime and the cyber threat landscape have been rapidly evolving in the past few years. In the beginning, the word “hacker” referred to someone who broke into systems just to show that they could. Now, to many people, the word “hacker” and the word “cybercriminal” are essentially synonymous.
As hacking has evolved into cybercrime, the cyber threats that most organizations experience are growing in sophistication. Cybercrime has become a business, and many organizations are not capable of standing up to professional cybercriminals.
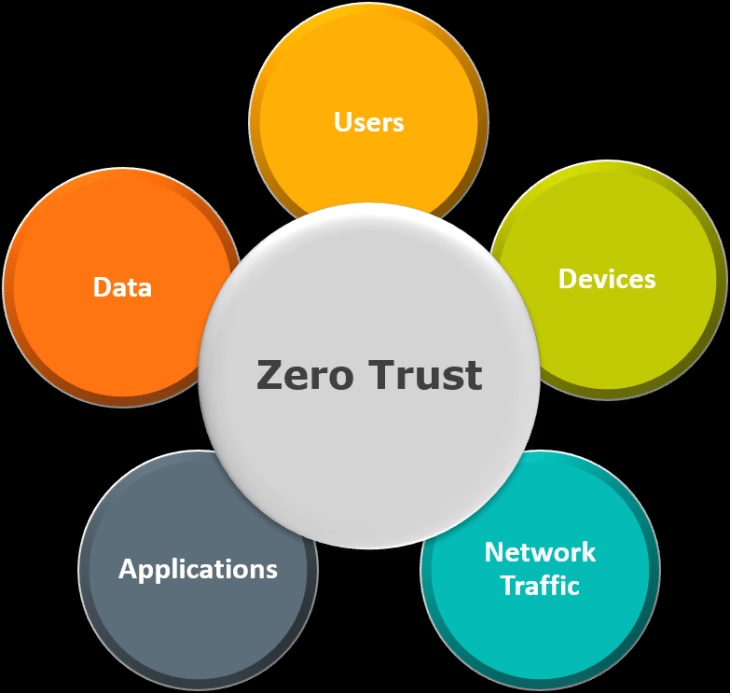
One of the reasons for this is that the majority of organizations operate based off of a perimeter-based security model, which is outdated and insecure. Effectively protecting an organization’s network requires a zero trust approach to security. Implementing zero trust security requires the ability to manage access and permissions for every user and resource in the network. Implementing this in an effective and scalable manner requires deploying a role-based access control (RBAC) solution.
The Dissolving Perimeter
Traditionally, many organizations have operated using a perimeter-based cybersecurity model. In this model, the organization assumes that everything within the organization’s network is benign and everything outside is potentially malicious. Since many organizations’ local area networks (LANs) only have a single point of connection with the public network, it is easy to enforce the “perimeter” and perform traffic inspection at the network boundary.
However, this model of network security is no longer valid. The network perimeter is eroding for several reasons, including the move to the cloud, remote work, and the increasing sophistication of cybercriminals. As organizations adopt cloud computing, the traditional perimeter-based model no longer makes sense. The organization’s cloud resources, which are considered part of the corporate network, are located outside the perimeter, on infrastructure not owned by the organization and accessible via the public Internet.
Remote work is another increasingly common use case that breaks the traditional perimeter model. In the past, most of an organization’s systems were desktops, which were consistently connected to the enterprise network. Now, laptops and mobile devices are increasingly common and operate on networks outside of the organization’s control and ability to monitor.
Finally, the traditional, perimeter-based model is breaking down because the assumption that organizations can secure their perimeter against attack is not valid. As cybercrime has become more professionalized, the average cyber threat has become a lot more dangerous. Cybercriminals have developed a set of extremely sophisticated methods for gaining access to an organization’s network, from stealing credentials with spear phishing emails to using social engineering. Cyber incidents are no longer a matter of “if” so much as “when”, and a perimeter-focused security model leaves organizations blind to threats already inside their network.
Introduction to Zero Trust Security
The failure of the perimeter model for cybersecurity has driven many organizations to pursue the zero trust security model. In a zero trust model, there is no assumption that anyone with access to an organization’s internal network is benign, legitimate, or who they are pretending to be.
Instead, zero trust security takes the “trust but verify” approach to security. When a user makes a request for a certain resource, their identity and right to access that resource is verified before the request is granted. This model dramatically decreases the damage that an attacker can do while moving laterally within an organization’s network since the organization has gained visibility into their internal network, something that does not exist with the perimeter-focused security model.
RBAC and Zero Trust
Zero trust security models are only effective if they are implemented well. If an organization needs to manually assign permissions to each user for each resource, the complexity of maintaining the security model grows exponentially. This is why role-based access control is so vital to zero trust security.
RBAC is designed to simplify permission management by assigning users to roles based upon their job functions. For example, a manager in the IT department may have two roles: as a manager and as a member of the IT department.
For assets within the organization’s network, different levels of permissions and access now be assigned based upon job roles. Instead of individually assigning permissions and access for each employee, a certain asset can be marked as only accessible to members of the financial department or C-level executives.
These decisions can be encoded as Boolean logic, enabling organizations to define rules more complex than a simple yes or no. When a user attempts to access a particular resource, their collection of roles is compared to the logic governing access. Based on the logic, they are either granted access or denied it, enabling an organization to enforce zero-trust access on their networks.
Securing Digital Assets
The cyber threat landscape is rapidly growing more dangerous. Cybercrime groups are increasingly sophisticated, and security models based upon keeping attackers outside of the organization’s network are no longer workable. A zero trust security model requires an organization to be able to validate a user’s identity and permissions before granting access to protected resources. RBAC enables an organization to define a simple, scalable method for describing and enforcing permissions on the organization’s network.
As the traditional perimeter-based security model becomes less applicable, an organization needs to implement zero trust security to minimize the impact of a potential incident. Managing access and permissions throughout the network via RBAC is the first step in accomplishing this.